If a message in the Message List has one or more attachments, an attachment icon ![]() will appear next to it, and the attachments pane will appear, just above the message body in the quick viewer, showing a list of all of the attachments.
will appear next to it, and the attachments pane will appear, just above the message body in the quick viewer, showing a list of all of the attachments.
Attachments can saved to your computer by dragging them from the pane and dropping them on the desktop or an open folder. Attachments in the form of a .EML file (i.e. an attached email) can also be dragged to a MailCOPA folder. There are also a variety of options available from the right-click context menu.”
NOTE that if you are viewing the text version of a message (where one was included by the original email software), and the HTML portion includes images, these will be shown here as attachments, and can thus be viewed. Attachments may also include such things as company logos.
There is also a similar pane above the body if you use the full viewer by opening the message.
WINMAIL.DAT files - These are produced by MS Outlook, and contain a rich-text version of the message, but can also contain attached files. If this is the case, MailCOPA will display these files in the Attachments Pane.
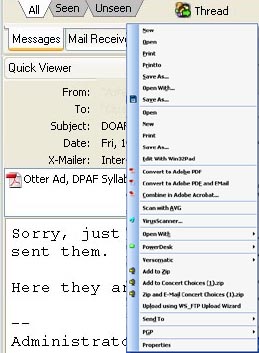
Right-clicking on an attachment will display a context menu, which is derived from Windows' settings (similar to the context menu you see when right-clicking on a file in a folder), with some appropriate additions. As we have no idea what options Windows will have created on your particular machine, you may find that we have duplicated some options, something we are unable to avoid.
Saving Files
Save – this will only appear if multiple attachments were selected when the context menu is opened – it will allow you to save the attachments, one at a time, to the selected destination folder, using their original names (with Windows duplicate checking). Note that you can also “Save Attachments” from the message window context menu – in which case, it will overwrite existing files of the same name without warning.
Save As – As above, but with the option of changing the file name on save. With multiple items selected, they will be saved one at a time.
Double-clicking on one of the icons will normally open the software configured on your machine to run such a file, and load the file into it (unless it is an image, in which case see Quick View.
Quick View – This provides a built-in viewer for .JPG and .GIF images, which may be preferable to loading up complex image software. Quick View will also be used when double-clicking the icon, if set up in Preferences ->Messages ->Viewing. Quick View has options for scrolling around the image, zooming and adjusting contrast/brightness (for the view only). To view the image in your preferred image software, you will need to use the Open option from the context menu (or double-click if you haven’t configured Quick View for that as shown above).
Open – This will open the file using the software configured on your system for that file type. If you do not have software installed for the file type, then Windows will ask what application should be used. Double-clicking the icon is the same as Open, except for image files, which will either open using your image software or Quick View –see above.
Properties – This displays the full file name of the attachment and the size of the file when it is decoded and saved in its native format. Note that because of the encoding methods used to include attachments in an email, the size within the email may be up to 30% bigger. Note this is not the same as the Windows File Properties, which you would get from the context menu from the saved file.
Beware of Malicious Attachments!
Email attachments are a common source of viruses (which can be very destructive) or trojans (which enable a hacker to use your machine for such things as distributing spam (Unsolicited Commercial Email) or mounting Distributed Denial of Service attacks). Some viruses, worms, macros, scripts and other malware can send themselves to people in the Outlook address book of an infected computer, so may come to you from familiar people, leading you to believe they are safe, so it is wise to scrutinise them carefully before opening. If you have a virus scanner installed, it is usually possible to virus scan an attachment immediately within MailCOPA, (from the context menu when an attachment is right-clicked) and it is wise to do this if you are in any doubt.
Potentially dangerous file types include: .COM, .EXE, .VBS, .PIF and you should also be suspicious of files with the .DOC extension - if they are Word 97 or later they may contain macros which can also be malicious.
Beware too of zip files (compressed files containing one or more original files) which may contain files of the above dangerous types, and which may not be detected by virus/malware scanners.
Attached web pages (.htm or .html files) can also be dangerous - they may contain code which exploits weaknesses in browsers (most often Internet Explorer). It is thus important to keep up to date with Windows security updates, but always treat such files with suspicion nevertheless.
In some circumstances, the true nature of an attachment may be hidden, by not showing the proper file extension (the characters after the last dot, or 'period'). Whatever the settings under Windows, MailCOPA will always show the full filenames and extensions. eg homepage.html.vbs will be shown in full.
Windows has a commonly used setting which hides file type extensions for known file types, which is a potential trap for the unwary. If you open Windows Explorer (right-click on the Start button and select Explore) and select from the menu View ![]() Folder Options and then the View tab, you will see an option "Hide file extensions for known file types" - if this is checked, then homepage.html.vbs will appear in Explorer and other places as homepage.html, thus concealing the fact that it is in fact a Visual Basic Script (potentially malicious), rather than a web page.
Folder Options and then the View tab, you will see an option "Hide file extensions for known file types" - if this is checked, then homepage.html.vbs will appear in Explorer and other places as homepage.html, thus concealing the fact that it is in fact a Visual Basic Script (potentially malicious), rather than a web page.